MULTISIG AND SDK SECURITY AUDITS FOR MYSTEN LABS
In the swiftly advancing digital realm, SDKs security has emerged as a crucial aspect for any technology-driven entity. Recognizing the paramount significance of ironclad security, Mysten Labs directed Blaize, a leader in the blockchain technology security domain, to ensure that their SDKs are not just compliant but also impeccable in terms of security standards.
ABOUT THE PROJECT
Mysten Labs is at the forefront of the web3 revolution. It is the foundational team behind the Sui blockchain, dedicated to empowering individuals and creators with unprecedented ownership over their data and content. Their mission is clear: to create secure, reliable, and mass-adoption-ready tools for the future of web3. The Mysten team combines extensive experience in building high-throughput organizations with scientific and engineering rigor to create trustworthy systems for an adversarial environment.
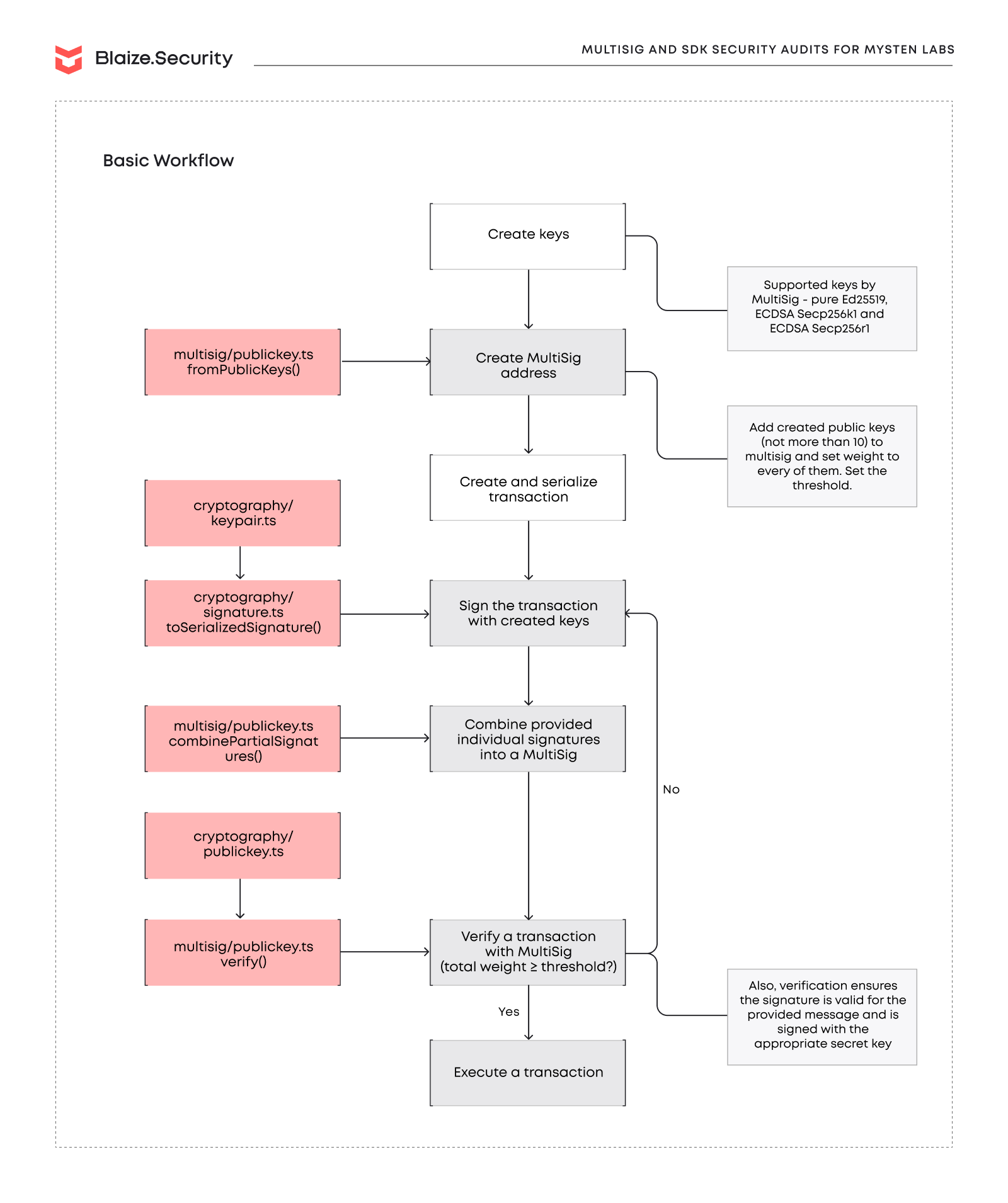
Mysten Labs, pushing the boundaries of digital innovation, had developed SDKs tailored to facilitate multi-signature transactions and personal message signing over the Sui blockchain. Given the sensitive nature of the transactions these SDKs would support, it was of paramount importance to ascertain their security integrity. Blaize, renowned for its prowess in blockchain technology, was brought on board to rigorously audit the security landscape of these SDKs.
MAIN REQUIREMENTS
During our audit, we scrutinized the codebase for various vulnerabilities in several stages:
1) Standard vulnerabilities checklists, including but not limited to:
- Transaction-ordering dependence
- Validation of input data
- Vulnerability for Denial-of-Service (DoS) attacks
- Malicious libraries and injections
- Storage issues (uninitialized, unused, etc) and incorrect local variables usage
- Correct processing of raw data (bitmaps and bytearrays)
- Cryptographic primitives review
and other potential vulnerabilities and attack vectors;
2) Business logic decompositions to find loopholes, deadlocks, hidden backdoors, incorrect math and calculations, malicious code injections and other flow related issues;
3) Review of dependencies, integrations and 3rd parties, verified with appropriate integration tests;
4) Our own internal security checklists, additionally verified during the testing stage. The team had the main focus on sustainability of the multisigs implementations against the incorrect data, on checks of correctness of cryptographic primitives usage, testing the cross-compatibility between Rust and TS multisig implementations, detection of deviations in multisig creation process.
SECURITY AUDIT PROCEDURE
Our audit processes encompassed manual and testing stages:
1.MANUAL AUDIT STAGE
- Manual line-by-line code by at least 2 security auditors with crosschecks and validation from the security lead;
- Protocol decomposition and components analysis with building an
- interaction scheme and sequence diagrams, depicting internal flows between the components
- Business logic inspection for potential loopholes, deadlocks, backdoors;
- Math operations and calculations analysis, formula modeling;
- Access control review, roles structure;
- Review of dependencies, 3rd parties, and integrations;
- Review with automated tools and static analysis;
Vulnerabilities analysis against several checklists, including internal Blaize.Security checklist;
- Storage usage review;
- Code quality, documentation, and consistency review.
For advanced components:
- Cryptographical elements and keys storage/usage audit;
- Review against OWASP recommendations;
- Blockchain interacting components and transactions flow;
- Review against CCSSA (C4) checklist and recommendations (if applicable);
2.TESTING STAGE
Development of edge cases based on manual stage results for false positives validation;
- Integration tests for checking connections with 3rd parties;
- Manual exploratory tests over the locally deployed protocol;
- Checking the existing set of tests and performing additional unit testing;
- Fuzzy and mutation tests (by request or necessity);
- End-to-end testing of complex systems;
Upon completion of the audit, we delivered a comprehensive security analysis reports to the Mysten Labs team. These reports included:
- Identified risks
- Potential mitigations
- Detailed vulnerability assessments
- Recommendations for improvements
SMART CONTRACT AUDIT IS A MUST FOR MAINTAINING SECURITY FOR YOUR PROJECT. DISCOVER MORE ON BLAIZE WEBSITE.
AUDIT RESULT
First Audit: The Sui TypeScript SDK, designed by Mysten Labs, championed multi-signature transactions, ensuring a more secure and flexible transaction-signing landscape. Leveraging renowned third-party libraries, this SDK stood as a testament to Mysten’s commitment to leveraging top-tier tools for optimum results. Blaize, in its rigorous audit, found the SDK to be largely robust. However, potential vulnerabilities were identified, including risks of DDoS attacks, outdated packages, and missing support structures. Blaize’s proactive approach resulted in a patch that addressed the majority of these issues, ensuring that the Mysten Labs’ Sui TypeScript SDK remains a paragon of security.
Second Audit: The Sui multisig Rust implementation further underscored Mysten Labs’ dedication to providing secure multi-signature solutions. It supported a diverse range of keys, ensuring flexibility and security. Post Blaize’s comprehensive audit, the SDK was found to be well-structured and self-declaring. Minor issues, mainly tied to validation oversights, were flagged and subsequently addressed. As a testament to its commitment to pushing for perfection, Blaize prepared and pushed another PR with identified issues patching for the multisig implementation in Sui repository.
In conclusion, the Mysten Labs multisig implementations demonstrate a commendable level of security, which Blaize has evaluated as “Highly Secure” with a score of 9.9 and 9.85 out of 10 relatively. While there are areas for improvement, particularly regarding documentation and certain security checks, the overall security and functionality of the SDK are robust. Blaize commends Mysten Labs for their commitment to security and looks forward to continued collaboration in enhancing the Sui TypeScript SDK and Rust toolkit.